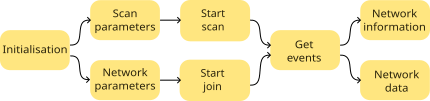
By the end of part 3, the WiFi chip was up & running, and as a simple test of WiFi operation, we’ll next scan the neighbourhood for WiFi networks, then attempt to join a network.
Scanning a network
As a quick check of wireless functionality, it can be useful to scan for WiFi networks within range. Before starting that, we need to send some IOCTL commands to configure various parameters, such as the network band.
The main problem with IOCTL calls is their sheer variety, that might require data in a specific format, or maybe no data at all. I haven’t been able to find a document that describes them, the only publicly-available documentation seems to be the source code . So when developing, it is quite possible to use the wrong IOCTL command, or send it the wrong data, and we need a way of reporting the error, without adding a lot of print function calls.
All my IOCTL functions return 0 if there wasn’t a reply, and -1 if the response indicated an error, so we can just chain commands using the short-circuit AND functionality to ensure execution will stop when an error occurs, and print the last IOCTL command that was executed:
#define IOCTL_WAIT 30 // Time to wait for ioctl response (msec)
const EVT_STR escan_evts[] = {EVT(WLC_E_ESCAN_RESULT), EVT(WLC_E_SET_SSID), EVT(-1)};
// Start a network scan
int scan_start(void)
{
int ret;
events_enable(escan_evts);
ret = ioctl_wr_int32(WLC_SET_SCAN_CHANNEL_TIME, IOCTL_WAIT, SCAN_CHAN_TIME) > 0 &&
ioctl_set_uint32("pm2_sleep_ret", IOCTL_WAIT, 0xc8) > 0 &&
ioctl_set_uint32("bcn_li_bcn", IOCTL_WAIT, 1) > 0 &&
ioctl_set_uint32("bcn_li_dtim", IOCTL_WAIT, 1) > 0 &&
ioctl_set_uint32("assoc_listen", IOCTL_WAIT, 0x0a) > 0 &&
ioctl_wr_int32(WLC_SET_BAND, IOCTL_WAIT, WIFI_BAND_ANY) > 0 &&
ioctl_wr_int32(WLC_UP, IOCTL_WAIT, 0) > 0;
ioctl_err_display(ret);
return(ret);
}
// Display last IOCTL if error
void ioctl_err_display(int retval)
{
IOCTL_MSG *msgp = &ioctl_txmsg;
IOCTL_HDR *iohp = (IOCTL_HDR *)&msgp->data[msgp->cmd.sdpcm.hdrlen];
char *cmds = iohp->cmd==WLC_GET_VAR ? "GET" :
iohp->cmd==WLC_SET_VAR ? "SET" : "";
char *data, *name;
if (retval <= 0)
{
data = (char *)&msgp->data[msgp->cmd.sdpcm.hdrlen+sizeof(IOCTL_HDR)];
name = iohp->cmd==WLC_GET_VAR || iohp->cmd==WLC_SET_VAR ? data : "";
printf("IOCTL error: cmd %lu %s %s\n", iohp->cmd, cmds, name);
}
}
We can check the code functioning by forcing an error, e.g. temporarily reducing the timeout value for a command such as ‘bcn_li_dtim’ to zero, in which case the code reports the following which, although somewhat terse, does indicate the source of the problem:
IOCTL error: cmd 263 SET bcn_li_dtim
To start a scan, we need one more IOCTL, with an data structure that sets some more parameters:
#define SSID_MAXLEN 32
#define SCANTYPE_ACTIVE 0
#define SCANTYPE_PASSIVE 1
#pragma pack(1)
typedef struct {
uint32_t version;
uint16_t action,
sync_id;
uint32_t ssidlen;
uint8_t ssid[SSID_MAXLEN],
bssid[6],
bss_type,
scan_type;
uint32_t nprobes,
active_time,
passive_time,
home_time;
uint16_t nchans,
nssids;
uint8_t chans[14][2],
ssids[1][SSID_MAXLEN];
} SCAN_PARAMS;
SCAN_PARAMS scan_params = {
.version=1, .action=1, .sync_id=0x1, .ssidlen=0, .ssid={0},
.bssid={0xff,0xff,0xff,0xff,0xff,0xff}, .bss_type=2,
.scan_type=SCANTYPE_PASSIVE, .nprobes=~0, .active_time=~0,
.passive_time=~0, .home_time=~0, .nchans=0
};
ioctl_set_data("escan", IOCTL_WAIT, &scan_params, sizeof(scan_params));
After that command is sent, we should receive several responses in the form of events; at least one from each WiFi network in range. The scan event handler has to byte-swap any 16 or 32-bit values, since they are in ‘network’ byte-order (big-endian); the handler function was described in the previous part of this blog.
It isn’t unusual for the same network to be reported more than once, e.g.
8C:59:73:xx:xx:xx 'Post_Office' chan 3
E8:65:D4:xx:xx:xx 'Court Hotel' chan 1
8C:59:73:xx:xx:xx 'Post_Office' chan 3
00:11:22:xx:xx:xx 'Virginia' chan 6
20:B0:01:xx:xx:xx 'vodafone' chan 6
6A:A2:22:xx:xx:xx '[hidden]' chan 6
..and so on..
In the tests I have done, the total time from power-up to receiving the last scan entry is around 2.1 seconds, which is surprisingly fast, considering how much chip-initialisation has been required.
Joining a network
This requires a large number of IOCTL commands to set up the WiFi interface, and there is little point in my listing all of them here, so I’m concentrating on specific settings of interest.
- Country: this is required in order to set domain-specific parameters. I’m taking the easy way out, and specifying a country code of ‘XX’, which is a common set of world-wide characteristics.
- Multicast: there is one MAC address set to 01:00:5E:00:00:FB which is the standard for IP v4
- Power saving: this is disabled by default, but can be compiled in if required, though it does significantly increase WiFi response times, as the device will sleep when idle, and takes some time to wake up & respond.
- Authentication: this uses a WPA2 pre-shared key, stored in plaintext, which is a major weakness in network security.
- Network name: the SSID is also stored as plaintext.
Once the network join has been initiated, we receive a stream of events to show progress. These can be viewed by calling set_display_mode with DISP_EVENT. A typical joining sequence might be:
Join secure network:
Rx_EVT 87 ASSOC_REQ_IE, flags 0, status 0, reason 0
Rx_EVT 3 AUTH, flags 0, status 0, reason 0
Rx_EVT 88 ASSOC_RESP_IE, flags 0, status 0, reason 0
Rx_EVT 7 ASSOC, flags 0, status 0, reason 0
Rx_EVT 16 LINK, flags 1, status 0, reason 0
Rx_EVT 1 JOIN, flags 0, status 0, reason 0
Rx_EVT 0 SET_SSID, flags 0, status 0, reason 0
Rx_EVT 46 PSK_SUP, flags 0, status 6, reason 0
..then Rx_DATA for broadcast/multicast network traffic..
Automatic reassociation after joining a network:
Rx_EVT 46 PSK_SUP, flags 0, status 6, reason 14
Rx_EVT 87 ASSOC_REQ_IE, flags 0, status 0, reason 0
Rx_EVT 3 AUTH, flags 0, status 0, reason 0
Rx_EVT 88 ASSOC_RESP_IE, flags 0, status 0, reason 0
Rx_EVT 9 REASSOC, flags 0, status 0, reason 0
Rx_EVT 16 LINK, flags 1, status 0, reason 0
Rx_EVT 46 PSK_SUP, flags 0, status 6, reason 0
Rx_EVT 1 JOIN, flags 0, status 0, reason 0
..then Rx DATA flow continues..
Join open network (no security):
Rx_EVT 87 ASSOC_REQ_IE, flags 0, status 0, reason 0
Rx_EVT 3 AUTH, flags 0, status 0, reason 0
Rx_EVT 88 ASSOC_RESP_IE, flags 0, status 0, reason 0
Rx_EVT 7 ASSOC, flags 0, status 0, reason 0
Rx_EVT 16 LINK, flags 1, status 0, reason 0
Rx_EVT 1 JOIN, flags 0, status 0, reason 0
Rx_EVT 0 SET_SSID, flags 0, status 0, reason 0
..then Rx_DATA for broadcast/multicast network traffic..
SSID not found:
Rx_EVT 0 SET_SSID, flags 0, status 3, reason 0
Password incorrect:
Rx_EVT 87 ASSOC_REQ_IE, flags 0, status 0, reason 0
Rx_EVT 3 AUTH, flags 0, status 0, reason 0
Rx_EVT 88 ASSOC_RESP_IE, flags 0, status 0, reason 0
Rx_EVT 7 ASSOC, flags 0, status 0, reason 0
Rx_EVT 16 LINK, flags 1, status 0, reason 0
Rx_EVT 1 JOIN, flags 0, status 0, reason 0
Rx_EVT 0 SET_SSID, flags 0, status 0, reason 0
Rx_EVT 46 PSK_SUP, flags 0, status 8, reason 15
Rx_EVT 46 PSK_SUP, flags 0, status 8, reason 14
..then the same sequence repeated..
The ‘status’ values are common to all the events:
- 0: success
- 3: no networks
- 6: unsolicited
- 8: partial
The ‘reason’ values are specific to an event, for example in PSK_SUP, 14 means that a de-authentication request has been received, and 15 indicates that a timeout of the pre-shared key handshake has occurred.
Also there is no guarantee that the events will arrive in this order; for example, when I tested on a different Access Point, the last 3 events were PSK_SUP, JOIN, and SET_SSID.
I have also tested the responses to network events:
Orderly shutdown of WiFi at the access point:
Rx_EVT 12 DISASSOC_IND, flags 0, status 0, reason 8
Rx_EVT 3 AUTH, flags 0, status 5, reason 0
Rx_EVT 46 PSK_SUP, flags 0, status 6, reason 0
Rx_EVT 16 LINK, flags 0, status 0, reason 2
Restore WiFi after orderly shutdown:
Rx_EVT 87 ASSOC_REQ_IE, flags 0, status 0, reason 0
Rx_EVT 3 AUTH, flags 0, status 0, reason 0
Rx_EVT 88 ASSOC_RESP_IE, flags 0, status 0, reason 0
Rx_EVT 9 REASSOC, flags 0, status 0, reason 0
Rx_EVT 16 LINK, flags 1, status 0, reason 0
Rx_EVT 46 PSK_SUP, flags 0, status 6, reason 0
Rx_EVT 1 JOIN, flags 0, status 0, reason 0
..then the data flow resumes..
Power-down of the access point:
Rx_EVT 16 LINK, flags 0, status 0, reason 1
Restore power to the access point:
Rx_EVT 16 LINK, flags 0, status 0, reason 1
Rx_EVT 87 ASSOC_REQ_IE, flags 0, status 0, reason 0
Rx_EVT 3 AUTH, flags 0, status 0, reason 0
Rx_EVT 88 ASSOC_RESP_IE, flags 0, status 0, reason 0
Rx_EVT 9 REASSOC, flags 0, status 0, reason 0
Rx_EVT 16 LINK, flags 1, status 0, reason 0
Rx_EVT 46 PSK_SUP, flags 0, status 6, reason 0
Rx_EVT 1 JOIN, flags 0, status 0, reason 0
..then the data flow resumes..
Network unavailable on startup:
Rx_EVT 0 SET_SSID, flags 0, status 3, reason 0
Network becomes available after startup:
Nothing!
Try to join a secure network, using no security
Rx_EVT 0 SET_SSID, flags 0, status 0, reason 0
So the good news is that the WiFi chip can automatically reconnect to the network under some circumstances, but the bad news is that it will not always reconnect, and I can find no single event showing if the device is connected or not. Rather than attempting to decode the events in detail, I’ve used an overall timeout for joining a network (default 10 seconds); if that fails there is a rest period (currently also 10 seconds) before the next re-connection attempt.
Example programs
There are two examples; see the introduction for details of how to re-build and run the code.
scan.c does a single scan, and returns a list of networks found. The result returned by the WiFi chip is displayed as-is, so may contain duplicates.
join.c joins a given network, reporting on progress; the network name and password must be entered in the source code:
#define SSID "testnet"
#define PASSWD "testpass"
The on-board LED flashes at 5 Hz prior to connection, and at 1 Hz when connected.
In the next part I’ll start using TCP/IP protocols.
| Project links | |
|---|---|
| Introduction | Project overview |
| Part 1 | Low-level interface; hardware & software |
| Part 2 | Initialisation; CYW43xxx chip setup |
| Part 3 | IOCTLs and events; driver communication |
| Part 4 | Scan and join a network; WPA security |
| Part 5 | ARP, IP and ICMP; IP addressing, and ping |
| Part 6 | DHCP; fetching IP configuration from server |
| Part 7 | DNS; domain name lookup |
| Part 8 | UDP server socket |
| Part 9 | TCP Web server |
| Part 10 | Web camera |
| Source code | Full C source code |
Copyright (c) Jeremy P Bentham 2022. Please credit this blog if you use the information or software in it.